Cinnaminson Homeowners: Discover the Easiest Way to Sell Your House
Many Cinnaminson residents find the idea of selling their house to evoke visions of many showings, expensive repairs, and prolonged discussions. Although for some people the conventional real estate market is efficient, it sometimes requires a large time, money, and emotional investment. But a lot easier, more direct option that suits especially those looking for speed and convenience is becoming more and more well-known. Choosing a direct house purchase from a specialist company buying homes in Cinnaminson, NJ presents a welcome change from the traditional approach and a straight route to a hassle-free transaction.
Bypass Costly Repairs and Renovations
Choosing a direct buyer is one of the most important benefits in terms of being able to sell your house as it is. This means you may totally avoid the sometimes costly and time-consuming chore of painting, remodelling bathrooms or kitchens, or even simple repairs. A direct buyer will usually buy your house “as-is,” whether it needs substantial structural repairs or little cosmetic enhancements.
Experience a Really Quick Sale
Operating on its own erratic schedule, the conventional real estate market Listings can last for weeks or months; after an offer is accepted, the closing procedure may be protracted because of inspections, appraisals, and financing conditions. For homeowners looking for speedy and effective asset liquidation, financial changes, or just a rapid relocation necessity, this expedited schedule is priceless. Investigating choices available at www.sellmyphillyhouse.com/we-buy-houses-cinnaminson-new-jersey/ can help one to see exactly how quickly a transaction may happen.
Cut Realtor Fees and Hidden Expenses
Realtor commissions, when sold through conventional methods, usually run from 5% to 6% of the transaction price, a sizable sum that reduces your equity. Besides, sellers may cover other charges, including marketing, staging, and closing fees. Usually non-existent with a direct house buyer are these costs.
Experience a straightforward, stress-free process
Selling to a direct home buyer is meant to be simple overall. Usually after corporate contact, they arrange a brief property tour. This simplified technique greatly lessens the emotional and practical strain usually related to selling a house. Visit www.sellmyphillyhouse.com/we-buy-houses-cinnaminson-new-jersey/. For further information on this easy procedure.
Get an advantage from dependability and certainty
Direct home buyers provide a great degree of surety, unlike conventional transactions that might collapse owing to buyer finance problems or cold feet. Usually working with cash, they save the time and effort required by significant loan processes or bank approvals. This dependability implies that, knowing the transaction will go as planned, once an offer is made and accepted, you may boldly schedule your following actions. Particularly while balancing other obligations in life, this peace of mind is quite priceless.
Investigating the possibility of a straight cash purchase has convincing benefits for Cinnaminson residents looking for the fastest and quickest approach to sell their house. This approach offers a stress-free way to sell your house on your terms by skipping repairs, speeding the schedule, removing fees, streamlining the process, and guaranteeing certainty.








































































 Are you trying to find the best nootropics? Outlook just provides the answer as to which choice is the better one. Every day, you have a lot on your mind! Each day, our brains produce tens of thousands of thoughts, some random, some informative, and some just motivated by boredom. But if you allow your thoughts to wander, you’ll lose productivity. Outlook details the top smart drugs. These
Are you trying to find the best nootropics? Outlook just provides the answer as to which choice is the better one. Every day, you have a lot on your mind! Each day, our brains produce tens of thousands of thoughts, some random, some informative, and some just motivated by boredom. But if you allow your thoughts to wander, you’ll lose productivity. Outlook details the top smart drugs. These 
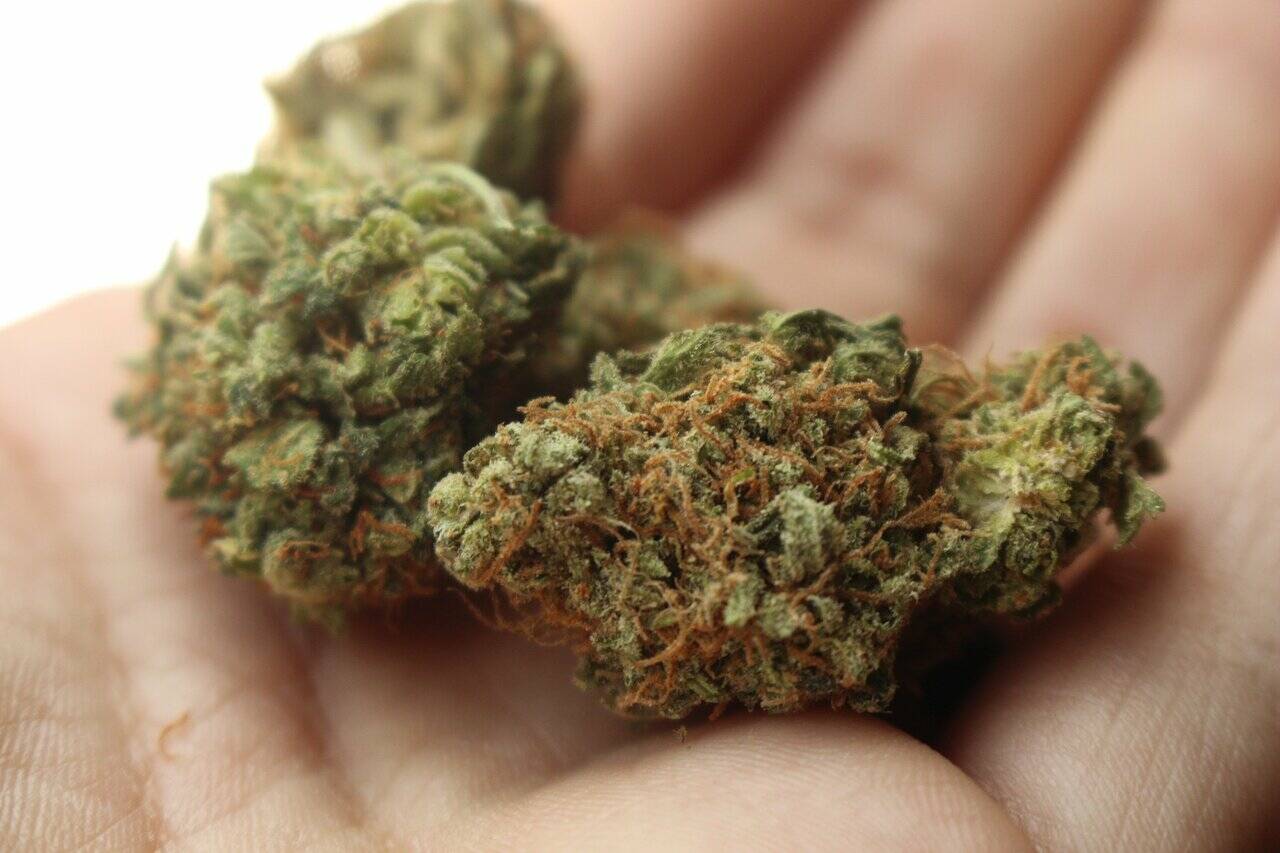
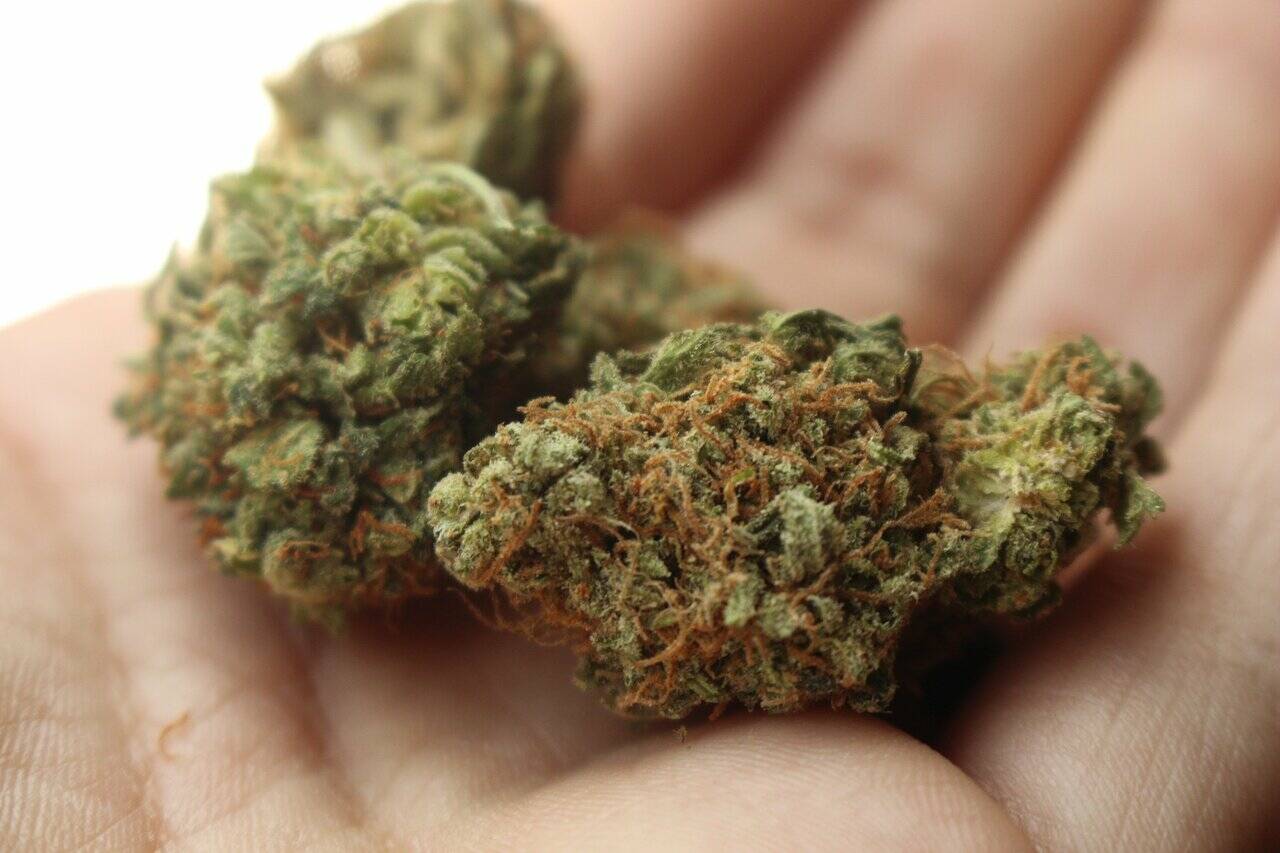
 Delta-8 THC Gummies are a delicious gummy candy that contain the derivative of Tetrahydrocannabinol. This legal product has been approved by California to provide a high THC content.
Delta-8 THC Gummies are a delicious gummy candy that contain the derivative of Tetrahydrocannabinol. This legal product has been approved by California to provide a high THC content.










 Is Delta-8 THC Legal?
Is Delta-8 THC Legal?

 Draw slowly and steadily:
Draw slowly and steadily: 













